Background
Boson Protocol is a decentralized infrastructure designed to facilitate the seamless exchange of digital assets (such as cryptocurrencies or NFTs) for real-world goods and services in a trustless and automated manner. It operates on blockchain technology, particularly the Ethereum network, and utilizes smart contracts to enable trust-minimized commerce.
Vision and Mission
Boson Protocol’s goal is to create a bridge between the digital and physical worlds using blockchain, enabling decentralized and trustless exchanges of value across those domains.
Key Features of Boson Protocol:
- Decentralized Commerce: It aims to disrupt traditional e-commerce by allowing users to buy physical goods and services through decentralized platforms without needing intermediaries like centralized marketplaces.
- Tokenized Vouchers: Boson uses non-fungible tokens (NFTs) to represent claims on physical goods or services. These tokens can be traded, transferred, or redeemed at a later point.
- Dispute Resolution: In case of disputes, Boson Protocol introduces a decentralized mechanism to resolve them based on predefined rules.
- Incentives for Participation: The protocol is built to incentivize participants (e.g., buyers, sellers, and dispute resolvers) through native tokens that reward their involvement in the system.
Audit Focus
The primary objective of this audit was to ensure that the smart contract system is secure, robust, and functions precisely as intended. The audit process was structured into three key areas:
- Security: Conducting a thorough analysis to identify any security vulnerabilities both within individual smart contracts and across the broader system of contracts.
- Architectural Soundness: Assessing the system’s architecture against industry-standard smart contract practices and general software engineering principles, ensuring the design is solid and adheres to best practices.
- Code Quality and Correctness: Performing a comprehensive review of the contract’s source code, with a focus on:
- Correctness: Ensuring the code behaves as expected.
- Readability: Evaluating the clarity and maintainability of the code.
- Complexity: Highlighting sections of the code that exhibit high complexity.
- Testing: Reviewing the extent and quality of test coverage to ensure the system has been rigorously tested.
This structured approach ensures the smart contract system meets stringent security, architectural, and quality standards.
Audit Insights
ImmuneBytes performed an in-depth audit of the Boson Protocol, identifying multiple high and low-severity vulnerabilities in the system. The Boson Protocol team acted promptly and effectively, resolving the issues swiftly. Their action and dedication to addressing these potential threats has reflected a strong commitment to ensuring the security of their protocol, creating a trustworthy environment for their users.
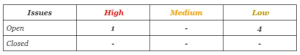
We have split the issues according to the severity levels:
- High severity issues will bring problems and should be fixed.
- Medium severity issues could potentially bring problems and should eventually be fixed.
- Low severity issues are minor details and warnings that can remain unfixed but would be better fixed at some point in the future.
The detailed audit report can be found here.
Key Findings
Function includes invalid access control
It refers to a vulnerability where a smart contract function is not properly restricted, allowing unauthorized users to access or execute it. A function in the contract allows the seller to admit to a fault and stop the deal. However, due to the absence of any such access modifier, anyone can trigger this function on behalf of the seller.
Recommendation: The function must include an onlyFromRouter() modifier to ensure that it can only be called from the router contract.
Use of Require statements should be preferred over if-else statements
In Solidity, require statements are preferred over if-else statements for handling validation and error checking due to their gas efficiency and clear transaction reversion. When a condition fails in a require statement, the transaction halts immediately, reverting any changes and refunding unused gas.
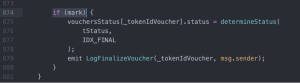
In the scenarios of strict validations, where the further execution of a function strictly depends on a value, it’s comparatively effective to use require statements instead of if statements.
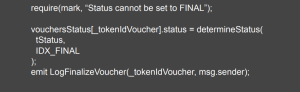
Recommendation: The validation in the triggerFinalizeVoucher() function, before updating the status of the voucher token, can be modified with a require statement as follows:
Adequate input or range validations not found
It refers to a situation where a smart contract fails to properly validate the inputs it receives from users or other contracts. Without input validation, malicious or unintended data can be passed into the contract, leading to unpredictable behavior or vulnerabilities such as overflows, underflows, or even unauthorized access. The setETHLimit() and setTokenLimit() in the TokenRegistry contract, do not implement proper input validations.
Recommendation: The above-mentioned functions should include effective validations to ensure no invalid uint argument is passed to the function.
Inadequate address validation before approval
It refers to a security vulnerability in smart contracts where the system fails to properly verify the legitimacy of an address before granting it access or permissions. This can occur when contracts allow users to register or approve addresses without thorough checks to ensure that the address is valid, authorized, or has not been flagged for suspicious activity. The approve() function in few places does not include zero address validations for the address being passed as arguments.
Recommendation: A require statement should be included in such functions to ensure no zero address is passed in the arguments.
Conclusion
In conclusion, the audit of the Boson Protocol by ImmuneBytes highlights the critical importance of thorough security assessments in the evolving landscape of decentralized finance. Through meticulous examination, several vulnerabilities were identified, and the Boson Protocol team’s swift response demonstrated their commitment to maintaining a secure and resilient platform. Their proactive measures not only addressed the identified issues but also reinforced the integrity of the protocol, fostering trust among users and stakeholders.
This case study underscores the significance of ongoing vigilance and continuous improvement in security practices, ensuring that DeFi protocols like Boson Protocol can operate safely and effectively in a rapidly changing environment.
